Sam Roberts' Twitter Account Hacked – Intimate Videos LEAKED!
Have you heard about the massive data breach involving Sam Roberts' Twitter account? The popular content creator recently fell victim to a sophisticated hacking attack that resulted in intimate videos being leaked online. This incident highlights the growing threat of cybercrime and the importance of protecting our digital identities. Let's dive deep into what happened, how it affects you, and what you can do to stay safe online.
Biography of Sam Roberts
Sam Roberts is a multifaceted content creator known for his diverse streaming content across multiple platforms. With a growing following on social media, Sam has built a reputation for sharing fitness routines, music playlists, cooking tutorials, and original content that resonates with his audience. His authentic approach to content creation has earned him a loyal fanbase who appreciate his transparency and creativity.
Personal Details and Bio Data:
- Solyluna24
- The Nude Truth About Room Dividers How Theyre Spicing Up Sex Lives Overnight
- The Turken Scandal Leaked Evidence Of A Dark Secret Thats Gone Viral
| Category | Information |
|---|---|
| Full Name | Sam Roberts |
| Known For | Streaming fitness, music, cooking, and original content |
| Social Media Handles | @samrobertssxm, @therealsamxfrank, @samxc63s |
| Nationality | Filipino (🇵🇭) |
| Content Style | Free, accessible content across multiple platforms |
| Recent Incident | Twitter account hacked, intimate videos leaked |
| Religious Affiliation | Christian (references "All glory to God") |
The Latest Posts from @samrobertssxm
The incident began when hackers gained unauthorized access to Sam Roberts' Twitter account (@samrobertssxm). According to reports, the attackers posted a massive 400GB dataset containing 2.873 billion Twitter (X) user records that were allegedly leaked in January 2025. This unprecedented breach has sent shockwaves through the online community, as it represents one of the largest data leaks in social media history.
The timing of this attack is particularly concerning, as it coincided with widespread layoffs at Twitter. A source close to the investigation revealed that the data was "almost certainly taken by a disgruntled employee while many employees were being laid off." This insider threat highlights the vulnerability of even the most secure systems when internal personnel are compromised or have malicious intent.
Stream Fitness, Music, Cooking, and Original Content—Completely Free
Sam Roberts built his brand around providing free, accessible content to his followers. His streaming platforms offered fitness tutorials, music playlists, cooking demonstrations, and original creative content without any paywall restrictions. This generous approach to content creation made him a beloved figure in the online community, but it also made him a target for cybercriminals looking to exploit his popularity.
- Cheapassgamer Twitter
- Leaked Tianastummys Nude Video Exposes Shocking Secret
- Leaked Porn Found In Peach Jars This Discovery Will Blow Your Mind
The hackers' decision to leak intimate videos from his account represents a particularly malicious form of attack, as it violates not only his privacy but also the trust he had built with his audience. Many of his followers expressed shock and disappointment at seeing personal content that was never intended for public consumption.
All Glory to God ✝️ @therealsamxfrank @samxc63s 🇵🇭
In the aftermath of the hack, Sam Roberts turned to his faith for strength, posting messages of resilience and gratitude. His religious references, including "All glory to God," demonstrate how he's coping with this violation of his privacy. The hacker's attack didn't just target his professional content but also invaded his personal life, making this a deeply traumatic experience.
Sam's Filipino heritage (🇵🇭) has also played a role in how he's processing this incident. Many of his followers from the Filipino community have rallied around him, offering support and solidarity during this difficult time. The cultural emphasis on family, community, and resilience has helped him maintain perspective despite the violation.
The 400GB Dataset Leak: What We Know
The scale of this data breach is staggering. The 400GB dataset contains 2.873 billion Twitter user records, representing a significant portion of the platform's user base. Cybersecurity experts are still analyzing the contents of the leak, but initial reports suggest that the data includes usernames, email addresses, phone numbers, and potentially sensitive personal information.
What makes this breach particularly alarming is the timing and method of the attack. The fact that it was allegedly carried out by a disgruntled employee during a period of mass layoffs suggests that even the most secure systems can be compromised from within. This incident serves as a wake-up call for companies to reassess their security protocols and employee vetting processes.
The Insider Threat: Disgruntled Employees and Data Breaches
The investigation into this massive data breach has revealed a troubling pattern. According to sources familiar with the matter, the data was "almost certainly taken by a disgruntled employee while many employees were being laid off." This insider threat represents one of the most dangerous forms of cyberattack, as employees often have legitimate access to sensitive systems and data.
When companies undergo mass layoffs, they create a perfect storm for insider threats. Employees who feel wronged or undervalued may seek revenge by stealing data, sabotaging systems, or selling confidential information to the highest bidder. In this case, the hacker appears to have taken advantage of the chaotic layoff period to exfiltrate massive amounts of data without detection.
Protecting Your Email Address: When to Share and When to Skip
The Sam Roberts incident highlights the importance of being cautious about where you share your personal information online. If it's your first and only visit to a website, there's no reason to hand over your email address unless absolutely necessary. Many websites use email collection as a way to build marketing lists or track user behavior, and in the wrong hands, this information can be used for malicious purposes.
Bugmenot: Skipping Unnecessary Email Requirements
One tool that many privacy-conscious users employ is Bugmenot, a service that lets you skip past unnecessary email requirements instantly. The platform maintains a database of shared login credentials for various websites, allowing users to access content without creating accounts or providing personal information.
The community has shared over 854,739 disposable logins for 320,365 websites through Bugmenot. This crowdsourced approach to privacy protection has become increasingly popular as users become more aware of the risks associated with sharing personal information online. If a login doesn't exist yet for a particular site, you can register a throwaway account and share it for others, creating a network of privacy-conscious users who help each other maintain anonymity online.
Understanding the Hacker's Motivation
Hackers target your email and social media accounts for various reasons, but the primary motivation is usually financial gain or personal satisfaction. Like your username and password, bank or credit card account numbers, or social security number, your personal information is valuable on the dark web. Cybercriminals can sell this data to other criminals or use it themselves for identity theft, financial fraud, or other illegal activities.
In Sam Roberts' case, the hackers may have had multiple motivations. The leak of intimate videos suggests a desire to humiliate and damage his reputation, while the massive data breach indicates a more organized criminal operation. The combination of personal attacks and large-scale data theft points to sophisticated cybercriminals who understand both the technical and psychological aspects of hacking.
The Consequences of Identity Theft and Cybercrime
If hackers get access to your personal information, they use it to commit identity theft, spread malware, or scam other people. The consequences can be devastating and long-lasting. Identity theft can ruin your credit score, lead to fraudulent charges on your accounts, and create legal problems that take years to resolve. Malware spread through compromised accounts can infect other users' devices, leading to a cascade of security problems across entire networks.
For content creators like Sam Roberts, the consequences extend beyond financial loss. The violation of privacy, the damage to reputation, and the emotional trauma of having intimate content exposed can be overwhelming. Many victims of hacking attacks report feeling violated, anxious, and unable to trust online platforms again.
How to Protect Yourself from Similar Attacks
The Sam Roberts incident serves as a reminder that anyone can be a target of cybercrime, regardless of their online presence or technical knowledge. Here are some practical steps you can take to protect yourself:
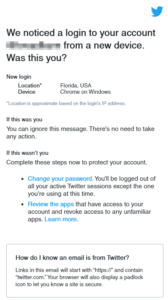
First, use strong, unique passwords for each of your online accounts. Password managers can help you generate and store complex passwords without having to remember them all. Enable two-factor authentication wherever possible, as this adds an extra layer of security even if your password is compromised.
Be cautious about the personal information you share online, especially on social media platforms. Review your privacy settings regularly and limit the amount of sensitive information that's publicly available. Be wary of phishing attempts, which often come in the form of emails or messages that appear to be from legitimate sources but are designed to trick you into revealing your login credentials.
Consider using disposable email addresses for websites and services that don't require your primary email. Services like Bugmenot can help you access content without creating accounts, reducing the number of places where your personal information is stored.
The Future of Online Privacy and Security
The massive data breach involving Sam Roberts' Twitter account is likely just the beginning of a new era of cybercrime. As more of our lives move online, the value of personal data continues to increase, making it an attractive target for criminals. Companies and individuals alike need to take a proactive approach to security, implementing robust protections and staying informed about the latest threats.
For content creators and public figures, the risks are even greater. The combination of public visibility and valuable personal information makes them prime targets for hackers. However, by implementing strong security measures and being cautious about information sharing, it's possible to significantly reduce the risk of falling victim to similar attacks.
Conclusion
The hacking of Sam Roberts' Twitter account and the subsequent leak of intimate videos serve as a stark reminder of the importance of online security in today's digital age. This incident, which involved the theft of 2.873 billion Twitter user records by a disgruntled employee, highlights the vulnerabilities that exist even in supposedly secure systems.
As we've seen, the consequences of such attacks can be devastating, ranging from identity theft and financial fraud to emotional trauma and reputation damage. However, by taking proactive steps to protect our personal information, using tools like Bugmenot to maintain privacy, and staying informed about the latest security threats, we can significantly reduce our risk of becoming victims of cybercrime.
The online community has rallied around Sam Roberts during this difficult time, demonstrating the power of solidarity in the face of cyber threats. As we move forward, let's use this incident as a learning opportunity to strengthen our own security practices and create a safer online environment for everyone. Remember, in the digital age, your personal information is your most valuable asset – protect it accordingly.